30
Blocking HTTPS (SSL) Domains with SSL Control
With Secure Socket Layer (SSL) Control it is possible to whitelist and blacklist HTTPS domains, as well as
other SSL services, based on keywords in their certificate. SSL control cannot be enforced at the group/user
level, only at the ZONE level. For example, if you enabled SSL control on the LAN zone, all users in the LAN
would have the same enforcement policies. However, SSL Control provides an excellent means to allow legit
SSL traffic while denying access to proxy sites that attempt to circumnavigate content filters or other
disallowed services.
SonicOS Enhanced firmware versions 4.0 and higher include SSL Control, a system for providing visibility into
the handshake of SSL sessions, and a method for constructing policies to control the establishment of SSL
connections. SSL is the dominant standard for the encryption of TCP-based network communications, with its
most common and well-known application being HTTPS (HTTP over SSL). SSL provides digital certificate-
based endpoint identification, and cryptographic and digest-based confidentiality to network communications.
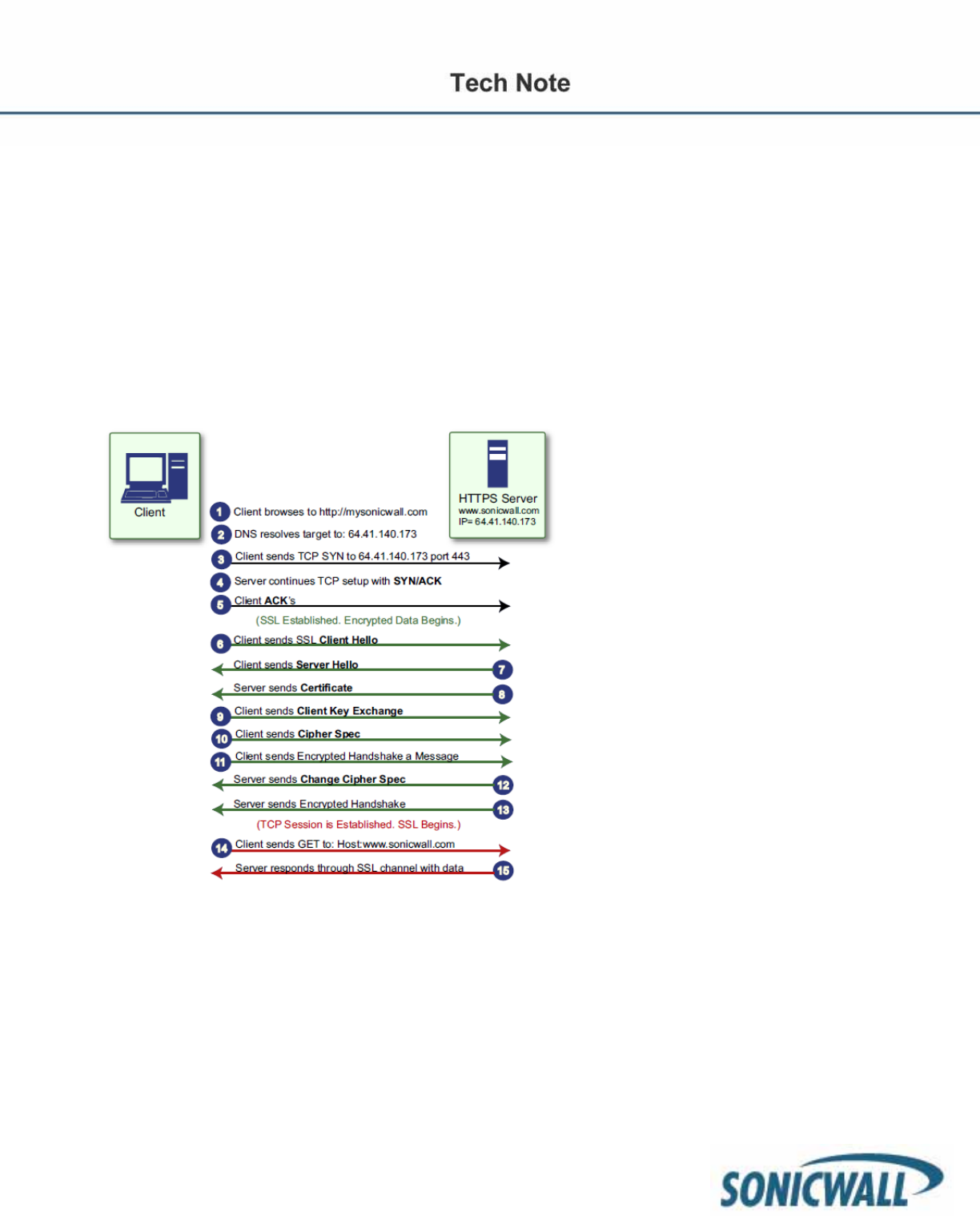
Below is a diagram that outlines the process of an SSL session.
An effect of the security provided by SSL is the obscuration of all payload, including the Uniform Resource
Locator (URL), for example, https://www.mysonicwall.com, being requested by a client when establishing an
HTTPS session. This is due to the fact that HTTP is transported within the encrypted SSL tunnel when using
HTTPS. It is not until the SSL session is established (Step 14) that the actual target resource
(www.mysonicwall.com) is requested by the client. But since the SSL session is already established, no
inspection of the session data by the firewall or any other intermediate device is possible. As a result, URL
based content filtering systems cannot consider the request to determine permissibility in any way other than
by IP address. While IP address-based filtering does not work well for unencrypted HTTP because of the
efficiency and popularity of Host-header based virtual hosting, IP filtering can work effectively for HTTPS due
to the rarity of Host-header based HTTPS sites. But this trust relies on the integrity of the HTTPS server
operator, and assumes that SSL is not being used for deceptive purposes. For the most part, SSL is
employed legitimately, being used to secure sensitive communications, such as online shopping, banking, or
any session where there is an exchange of personal or valuable information. The


















