ProSecure Unified Threat Management UTM10 or UTM25 Reference Manual
Firewall Protection 5-5
v1.0, September 2009
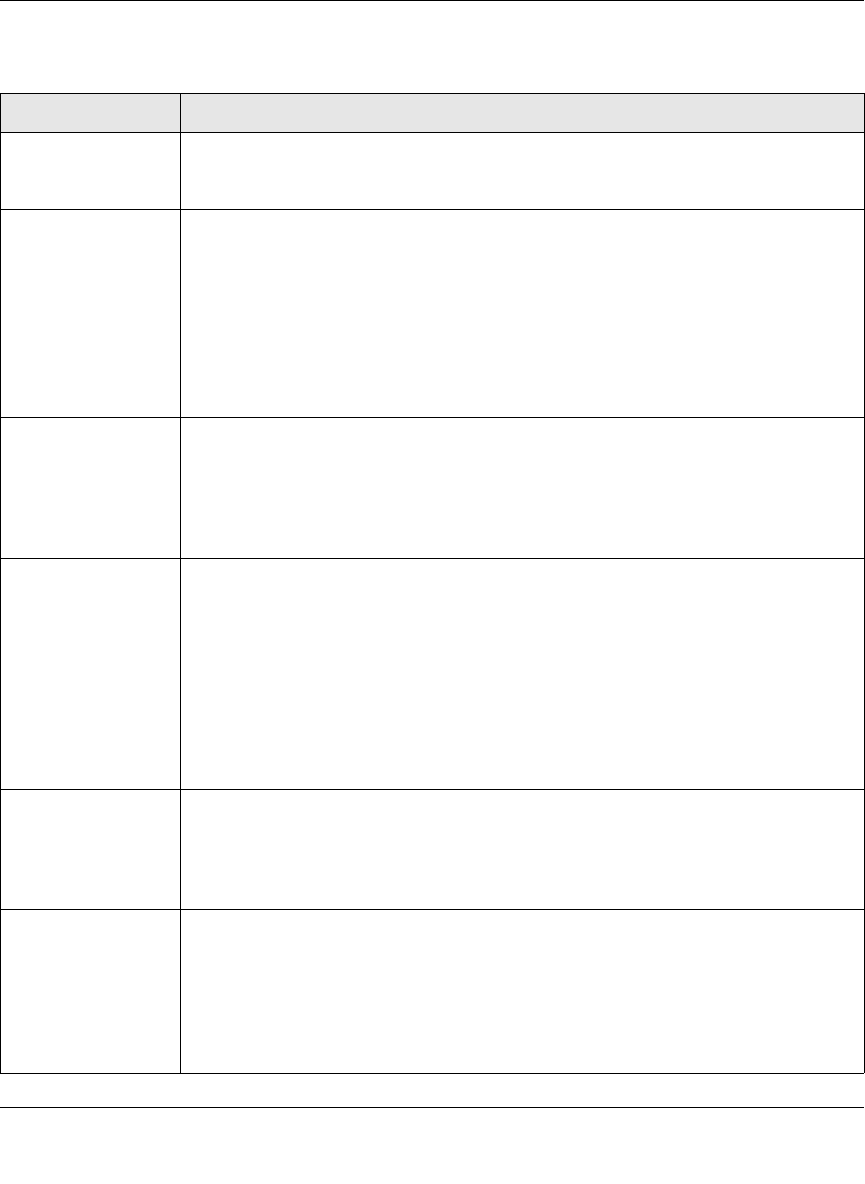
Table 5-2. Outbound Rules Overview
Setting Description (or Subfield and Description)
Service The service or application to be covered by this rule. If the service or application does
not appear in the list, you must define it using the Services menu (see “Adding
Customized Services” on page 5-30).
Action (Filter) The action for outgoing connections covered by this rule:
• BLOCK always.
• BLOCK by schedule, otherwise allow.
• ALLOW always.
• ALLOW by schedule, otherwise block.
Note: Any outbound traffic that is not blocked by rules you create is allowed by the
default rule.
ALLOW rules are only useful if the traffic is already covered by a BLOCK rule. That
is, you wish to allow a subset of traffic that is currently blocked by another rule.
Select Schedule The time schedule (that is, Schedule1, Schedule2, or Schedule3) that is used by this
rule.
• This pull-down menu is activated only when “BLOCK by schedule, otherwise allow”
or “ALLOW by schedule, otherwise block” is selected as the Action.
• Use the schedule screen to configure the time schedules (see “Setting a Schedule
to Block or Allow Specific Traffic” on page 5-39).
LAN Users The settings that determine which computers on your network are affected by this
rule. The options are:
• Any. All PCs and devices on your LAN.
• Single address. Enter the required address to apply the rule to a single device on
your LAN.
• Address range. Enter the required addresses in the Start and Finish fields to apply
the rule to a range of devices.
• Groups. Select the Group to which the rule applies. Use the LAN Groups screen
(under Network Configuration) to assign PCs to Groups. See “Managing Groups
and Hosts (LAN Groups)” on page 4-12.
WAN Users The settings that determine which Internet locations are covered by the rule, based
on their IP address. The options are:
• Any. All Internet IP address are covered by this rule.
• Single address. Enter the required address in the start field.
• Address range. Enter the Start and Finish fields.
DMZ Users The settings that determine which DMZ computers on the DMZ network are affected
by this rule. The options are:
• Any. All PCs and devices on your DMZ network.
• Single address. Enter the required address to apply the rule to a single PC on the
DMZ network.
• Address range. Enter the required addresses in the Start and Finish fields to apply
the rule to a range of DMZ computers.


















