ProSecure Unified Threat Management UTM10 or UTM25 Reference Manual
11-8 Monitoring System Access and Performance
v1.0, September 2009
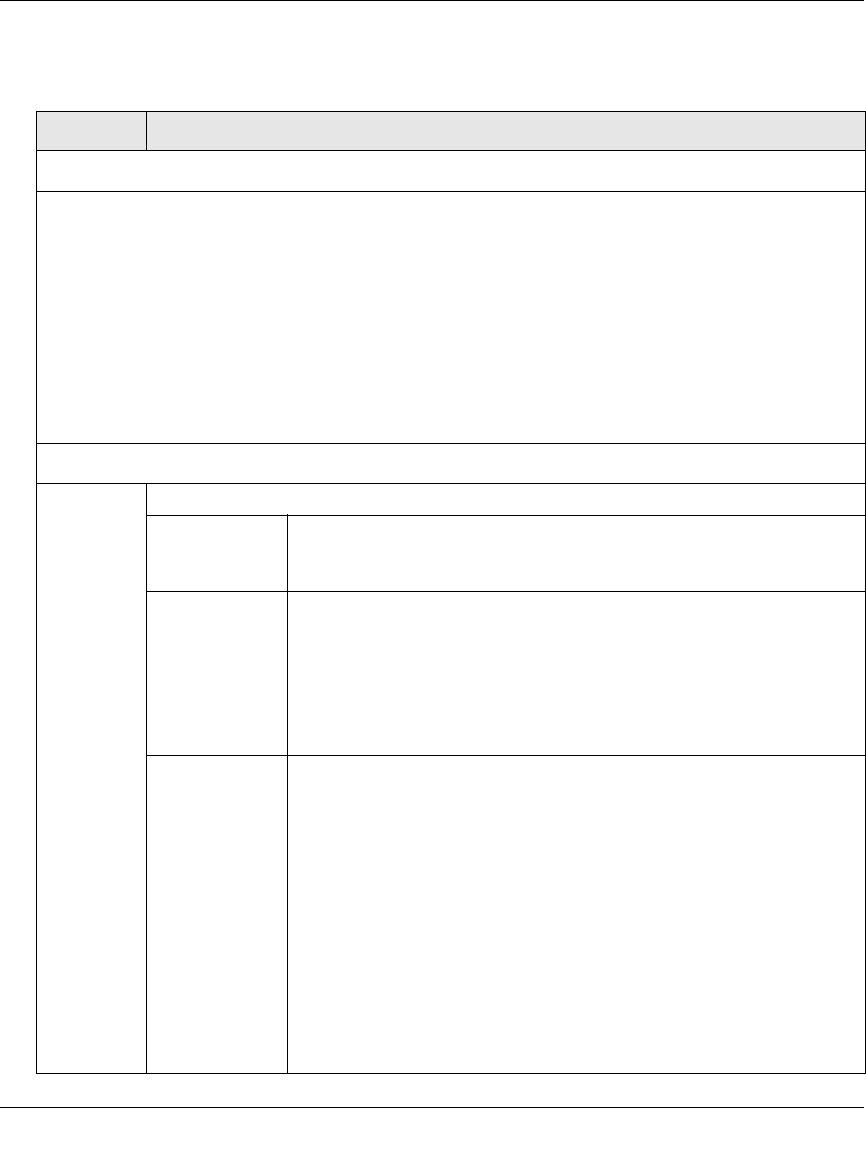
2. Enter the settings as explained in Table 11-2.
Table 11-3. E-mail and Syslog Settings
Setting Description (or Subfield and Description)
System Logs Option
Select the checkboxes to specify which system events are logged:
• Change of Time by NTP. Logs a message when the system time changes after a request from an
NTP server.
• Secure Login Attempts. Logs a message when a secure login is attempted. Both, successful and
failed login attempts are logged.
• Reboots. Logs a message when the UTM has been rebooted through the Web Management
Interface. (No message is logged when the Reset button has been pushed to reboot the UTM.)
• All Unicast Traffic. All incoming unicast packets are logged.
• All Broadcast/Multicast Traffic. All incoming broadcast and multicast packets are logged.
• WAN Status. WAN link-status related events are logged.
• Resolved DNS Names. All resolved DNS names are logged.
Email Logs to Administrator
Enable Select this checkbox to enable the UTM to send a log file to an e-mail address.
Send to The e-mail address of the recipient of the log file.
Click Send Now to immediately send the logs that you first must have
specified below.
Frequency Select a radio button to specify how often the log file is sent:
• When the space is full. Logs are sent when the storage space that is
assigned to the logs is full.
• Daily. Logs are sent daily at the time that you specify from the pull-
down menus (hours and minutes).
• Weekly. Logs are sent weekly at the day and time that you specify
from the pull-down menus (weekday, hours, and minutes).
Select Logs to
Send
Select the checkboxes to specify which logs are sent via e-mail:
• System Logs. The system event logs that you have specified in the
System Logs Options section at the top of the screen. However, by
default, many more types of events are logged in the system logs.
• Traffic Logs. All scanned incoming and outgoing traffic.
• Malware Logs. All intercepted viruses and malware threats.
• Spam Logs. All intercepted spam.
• IM/P2P Logs. All instant messaging and peer-to-peer access
violations.
• Email filter Logs. All e-mails that are blocked because of file
extension and keyword violations.
• Firewall Logs. The firewall logs that you have specified on the
Firewall Logs screen (see “Configuring and Activating Firewall Logs”
on page 11-13).


















