ProSecure Unified Threat Management UTM10 or UTM25 Reference Manual
11-32 Monitoring System Access and Performance
v1.0, September 2009
Querying Logs and Generating Reports
The extensive logging and reporting functions of the UTM let you perform the following tasks that
help you to monitor the protection of the network and the performance of the UTM:
• Querying and downloading logs
• Generating and downloading e-mail, Web, and system reports
• Scheduling automatic e-mail, Web, and system reports, and e-mailing these reports to
specified recipients.
For information about e-mailing logs and sending logs to a syslog server, see “Configuring and
Activating System, E-mail, and Syslog Logs” on page 11-6.
Querying the Logs
The UTM generates logs that provide detailed information about malware threats and traffic
activities on the network. You can view these logs through the Web Management Interface or save
the log records in CSV or HTML format and download them to a computer (the downloading
option is not available for all logs).
The UTM provides 13 types of logs:
• Traffic Logs. All scanned incoming and outgoing traffic.
• Spam Logs. All intercepted spam.
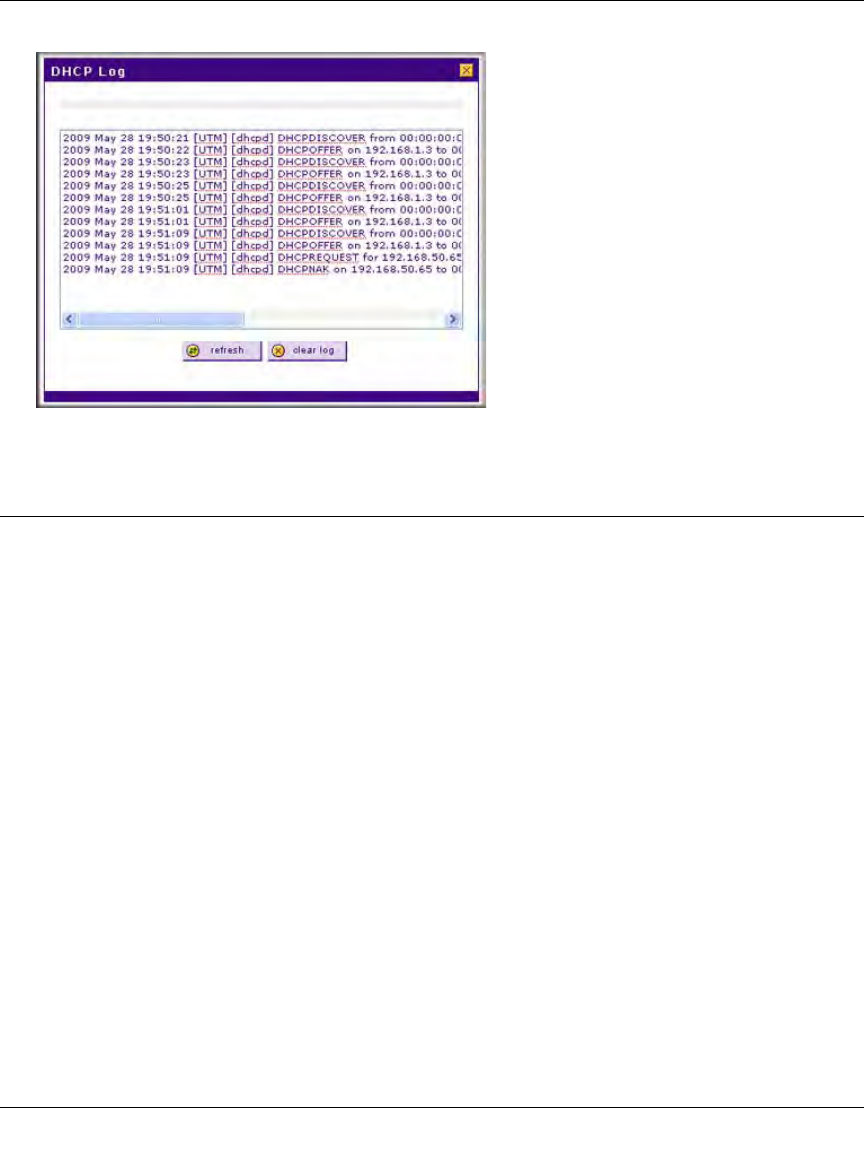
Figure 11-22


















