ProSecure Unified Threat Management UTM10 or UTM25 Reference Manual
Firewall Protection 5-21
v1.0, September 2009
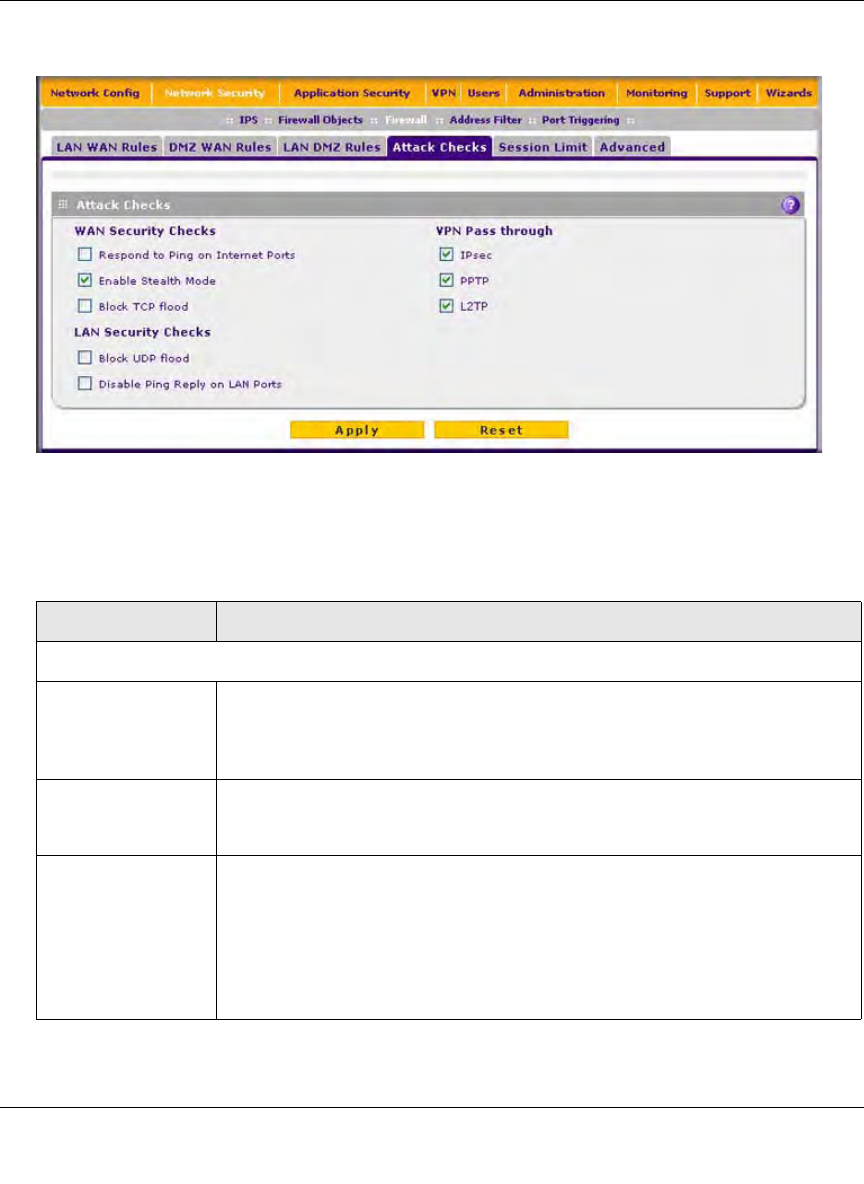
2. Click the Attack Checks submenu tab. The Attack Checks screen displays.
3. Enter the settings as explained in Table 5-4.
Figure 5-11
Table 5-4. Attack Checks Settings
Setting Description (or Subfield and Description)
WAN Security Checks
Respond To Ping On
Internet Ports
Select the Respond To Ping On Internet Ports checkbox to enable the UTM to
respond to a ping from the Internet. A ping can be used as a diagnostic tool.
Keep this checkbox deselected unless you have a specific reason to enable the
UTM to respond to a ping from the Internet.
Enable Stealth Mode Select the Enable Stealth Mode checkbox (which is the default setting) to
prevent the UTM from responding to port scans from the WAN, thus making it
less susceptible to discovery and attacks.
Block TCP Flood Select the Block TCP Flood checkbox to enable the UTM to drop all invalid
TCP packets and to protect the UTM from a SYN flood attack.
A SYN flood is a form of denial of service attack in which an attacker sends a
succession of SYN requests to a target system. When the system responds, the
attacker does not complete the connections, thus leaving the connection half-
open and flooding the server with SYN messages. No legitimate connections
can then be made. By default, the Block TCP Flood checkbox is deselected.


















