Reference Manual for the Model FVS318 Cable/DSL ProSafe VPN Firewall
6-2 Virtual Private Networking
WhatisaVPN
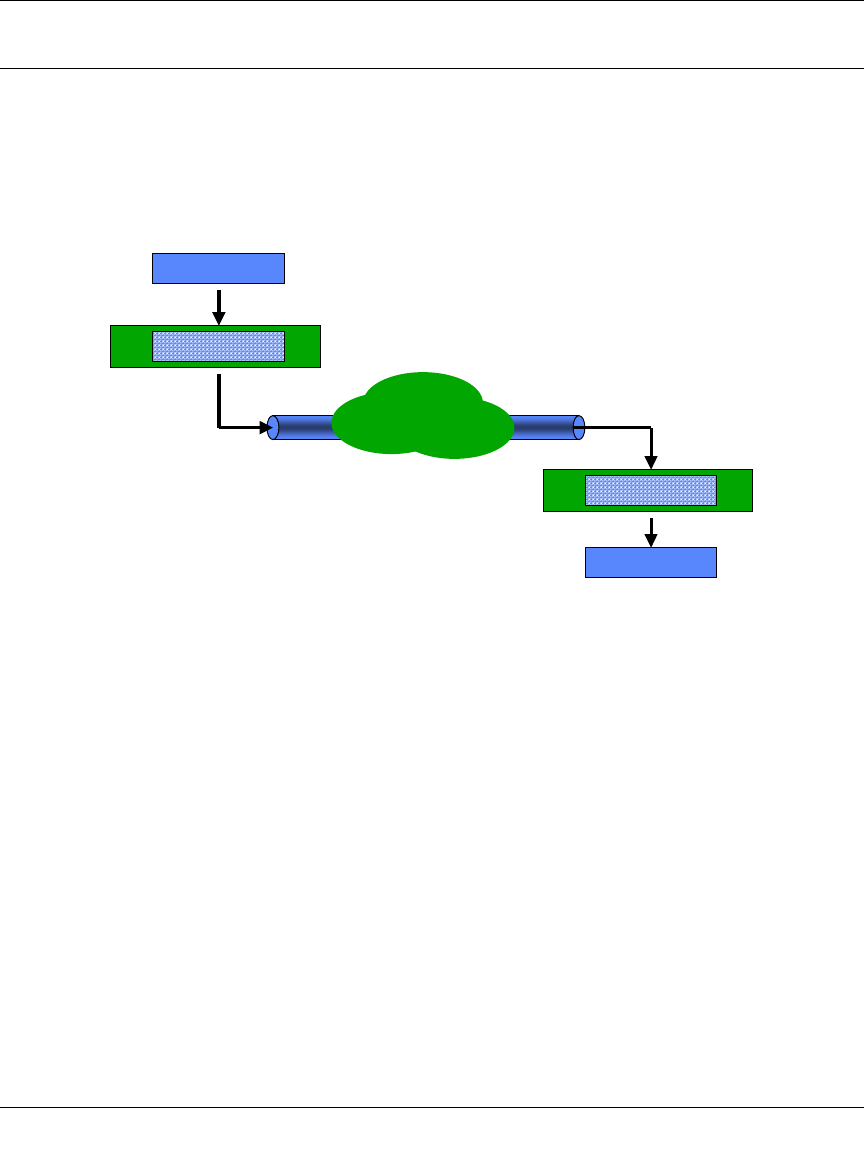
A VPN can be thought of as a secure tunnel passing through the Internet, connecting two devices
such as a PC or router, which form the two tunnel endpoints. At one endpoint, data is encapsulated
and encrypted, then transmitted through the Internet. At the far endpoint, the data is received,
unencapsulated and decrypted. Although the data may pass through several Internet routers
between the endpoints, the encapsulation and encryption forms a virtual “tunnel” for the data.
The tunnel endpoint device, which encodes or decodes the data, can either be a PC running VPN
client software or a VPN-enabled router or server. Several software standards exist for VPN data
encapsulation and encryption, such as PPTP and IPSec. Your FVS318 VPN Firewall uses IPSec.
To set up a VPN connection, you must configure each endpoint with specific identification and
connection information describing the other endpoint. This set of configuration information
defines a security association (SA) between the two points. The FVS318 is capable of eight
Security Associations.
Two common applications of VPN are
• secure access from a remote PC, such as a telecommuter connecting to an office network
• secure access between two networks, such as a branch office and a main office
These applications are described below.
DATA PACKET
ENCRYPTION AND ENCAPSULATION
UNENCAPSULATION AND DECRYPTION
INTERNET
TRANSMISSION
VIA INTERNET
DATA PACKET


















