Chapter 6 Device Security Settings
Vantage CNM User’s Guide
124
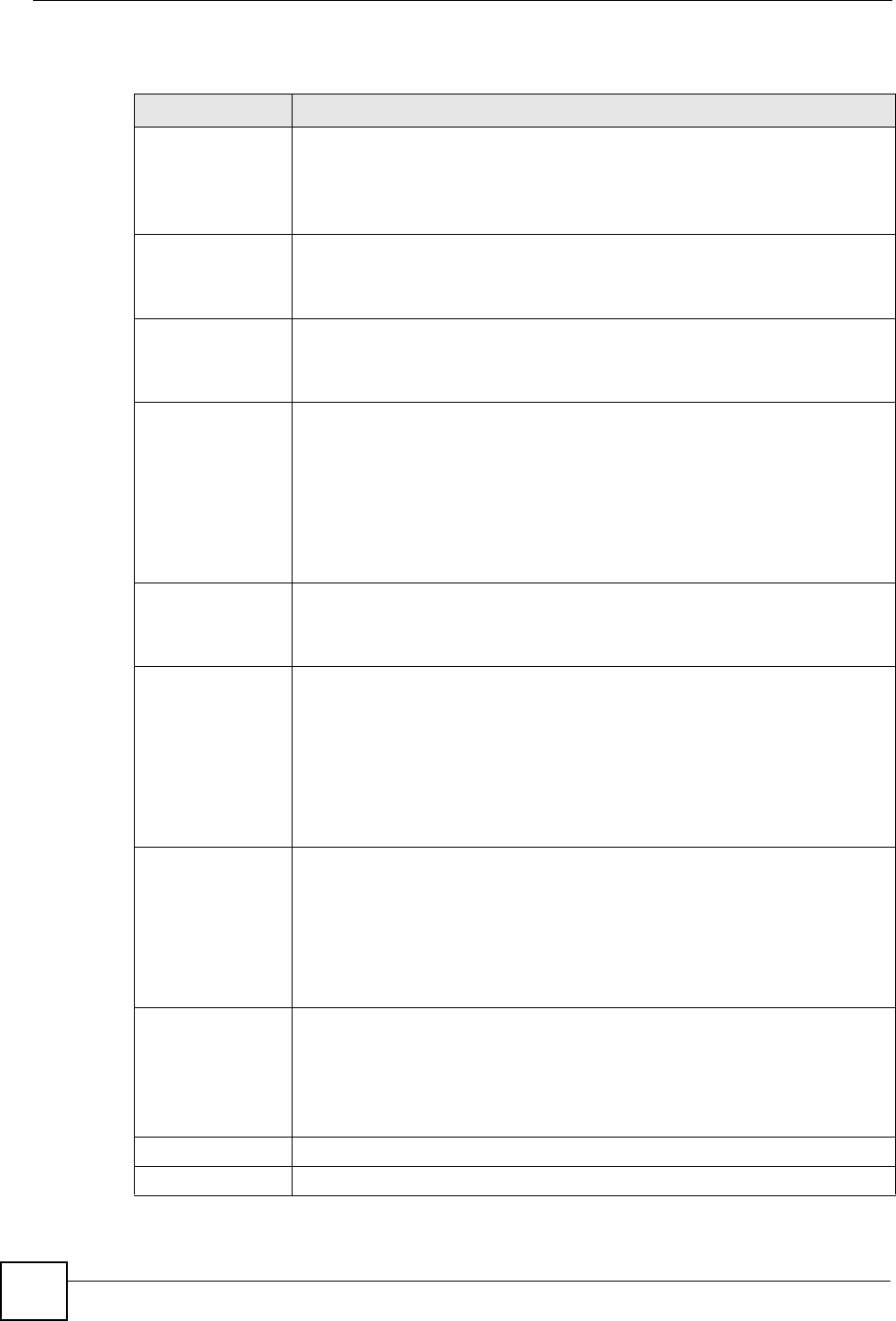
The following table describes the labels in this screen.
Table 46 Device Operation > Device Configuration > Security > Firewall > Threshold
LABEL DESCRIPTION
Disable DoS Attack
Protection on
Select the interface(s) (or VPN tunnels) for which you want the device to not use
the Denial of Service protection thresholds. This disables DoS protection on the
selected interface (or all VPN tunnels).
You may want to disable DoS protection for an interface if the device is treating
valid traffic as DoS attacks. Another option would be to raise the thresholds.
Denial of Service
Thresholds
The device measures both the total number of existing half-open sessions and
the rate of session establishment attempts. Both TCP and UDP half-open
sessions are counted in the total number and rate measurements. Measurements
are made once a minute.
One Minute Low
This is the rate of new half-open sessions per minute that causes the firewall to
stop deleting half-open sessions. The device continues to delete half-open
sessions as necessary, until the rate of new connection attempts drops below this
number.
One Minute High
This is the rate of new half-open sessions per minute that causes the firewall to
start deleting half-open sessions. When the rate of new connection attempts rises
above this number, the device deletes half-open sessions as required to
accommodate new connection attempts.
For example, if you set the one minute high to 100, the device starts deleting half-
open sessions when more than 100 session establishment attempts have been
detected in the last minute. It stops deleting half-open sessions when the number
of session establishment attempts detected in a minute goes below the number
set as the one minute low.
Maximum
Incomplete Low
This is the number of existing half-open sessions that causes the firewall to stop
deleting half-open sessions. The device continues to delete half-open requests
as necessary, until the number of existing half-open sessions drops below this
number.
Maximum
Incomplete High
This is the number of existing half-open sessions that causes the firewall to start
deleting half-open sessions. When the number of existing half-open sessions
rises above this number, the device deletes half-open sessions as required to
accommodate new connection requests. Do not set Maximum Incomplete High
to lower than the current Maximum Incomplete Low number.
For example, if you set the maximum incomplete high to 100, the device starts
deleting half-open sessions when the number of existing half-open sessions rises
above 100. It stops deleting half-open sessions when the number of existing half-
open sessions drops below the number set as the maximum incomplete low.
TCP Maximum
Incomplete
An unusually high number of half-open sessions with the same destination host
address could indicate that a DoS attack is being launched against the host.
Specify the number of existing half-open TCP sessions with the same destination
host IP address that causes the firewall to start dropping half-open sessions to
that same destination host IP address. Enter a number between 1 and 256. As a
general rule, you should choose a smaller number for a smaller network, a slower
system or limited bandwidth. The device sends alerts whenever the TCP
Maximum Incomplete is exceeded.
Blocking Time
Select the action that the device takes when the TCP maximum incomplete
threshold is reached.
Select the check box if you want the device to deny new connection requests for
the number of minutes that you specify (between 1 and 255).
Clear the check box if you want the device to delete the oldest half open session
when a new connection request comes.
Apply Click Apply to save your changes back to the device.
Reset Click Reset to begin configuring this screen afresh.


















