Chapter 6 Device Security Settings
Vantage CNM User’s Guide
160
6.9.2 Intrusion Severity
Intrusions are assigned a severity level based on the following table. The intrusion severity
level then determines the default signature action.
6.9.3 Signature Actions
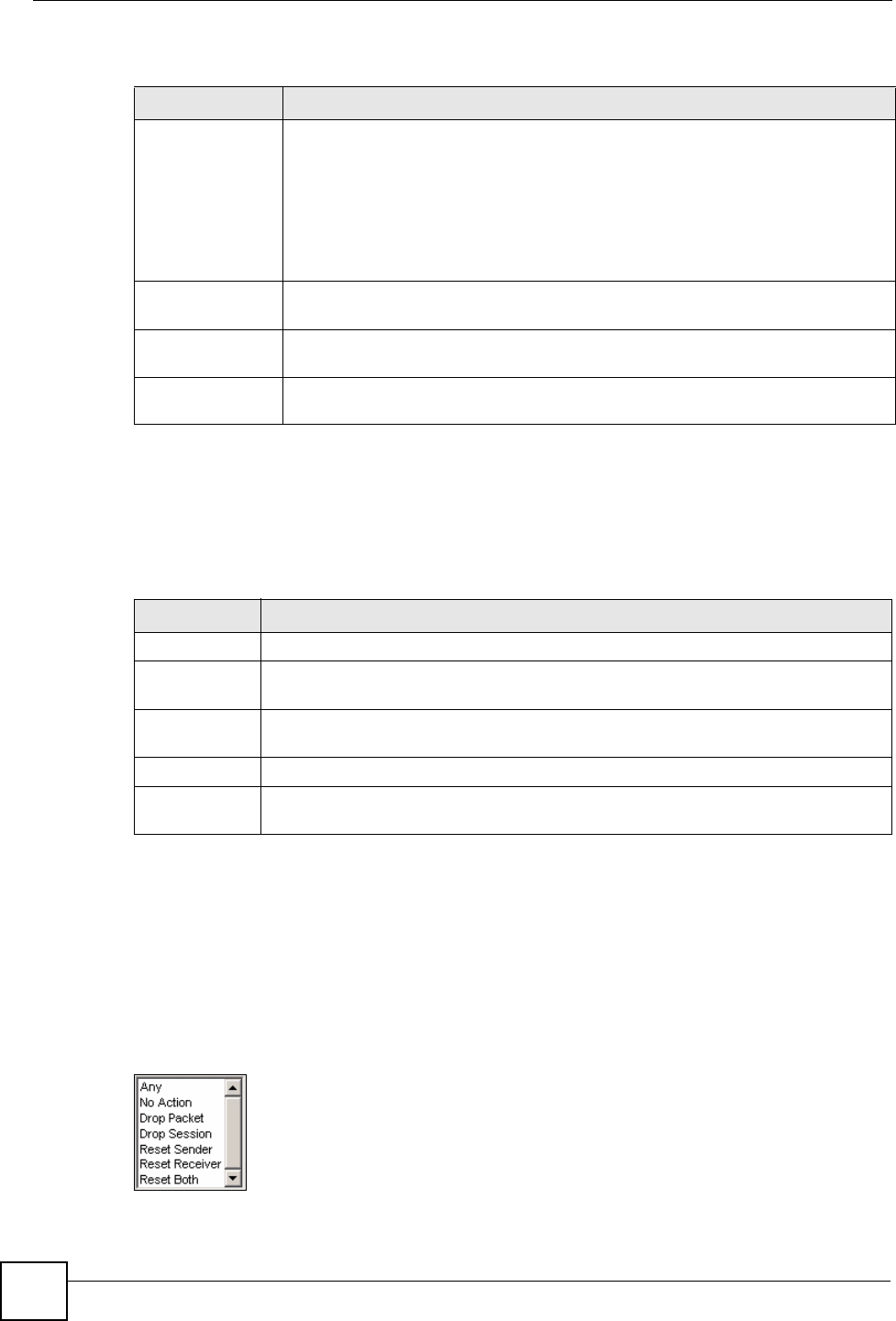
You can enable/disable individual signatures. You can log and/or have an alert sent when
traffic meets a signature criteria. You can also change the default action to be taken when a
packet or stream matches a signature. The following figure and table describes these actions.
Note that in addition to these actions, a log may be generated or an alert sent, if those check
boxes are selected and the signature is enabled.
Figure 73 Device Operation > Device Configuration > Security > IDP > Signature > Actions
VirusWorm A computer virus is a small program designed to corrupt and/or alter the operation
of other legitimate programs. A worm is a program that is designed to copy itself
from one computer to another on a network. A worm’s uncontrolled replication
consumes system resources thus slowing or stopping other tasks.
The IDP VirusWorm category refers to network-based viruses and worms. The
Anti-Virus (AV) screen refers to file-based viruses and worms. Refer to the anti-
virus chapter for additional information on file-based anti-virus scanning in the
device.
Porn The device can block web sites if their URLs contain certain pornographic words. It
cannot block web pages containing those words if the associated URL does not.
WebAttacks Web attack signatures refer to attacks on web servers such as IIS (Internet
Information Services).
SPAM Spam is unsolicited "junk" e-mail sent to large numbers of people to promote
products or services. Refer to the anti-spam chapter for more detailed information.
Table 62 Device Operation > Device Configuration > Security > IDP > Signature > Attack
Types (continued)
TYPE DESCRIPTION
Table 63 Device Operation > Device Configuration > Security > IDP > Signature > Intrusion
Severity
SEVERITY DESCRIPTION
Severe These are intrusions that try to run arbitrary code or gain system privileges.
High These are known serious vulnerabilities or intrusions that are probably not false
alarms.
Medium These are medium threats, access control intrusions or intrusions that could be false
alarms.
Low These are mild threats or intrusions that could be false alarms.
Very Low These are possible intrusions caused by traffic such as Ping, trace route, ICMP
queries etc.


















