Chapter 30 IDP
ZyWALL USG 50 User’s Guide
491
30.6.3 IDP Service Groups
An IDP service group is a set of related packet inspection signatures.
Scan A scan describes the action of searching a network for an exposed
service. An attack may then occur once a vulnerability has been
found. Scans occur on several network levels.
A network scan occurs at layer-3. For example, an attacker looks for
network devices such as a router or server running in an IP network.
A scan on a protocol is commonly referred to as a layer-4 scan. For
example, once an attacker has found a live end system, he looks for
open ports.
A scan on a service is commonly referred to a layer-7 scan. For
example, once an attacker has found an open port, say port 80 on a
server, he determines that it is a HTTP service run by some web
server application. He then uses a web vulnerability scanner (for
example, Nikto) to look for documented vulnerabilities.
Buffer Overflow A buffer overflow occurs when a program or process tries to store
more data in a buffer (temporary data storage area) than it was
intended to hold. The excess information can overflow into adjacent
buffers, corrupting or overwriting the valid data held in them.
Intruders could run codes in the overflow buffer region to obtain
control of the system, install a backdoor or use the victim to launch
attacks on other devices.
Virus/Worm A computer virus is a small program designed to corrupt and/or alter
the operation of other legitimate programs. A worm is a program that
is designed to copy itself from one computer to another on a network.
A worm’s uncontrolled replication consumes system resources, thus
slowing or stopping other tasks.
Backdoor/Trojan A backdoor (also called a trapdoor) is hidden software or a hardware
mechanism that can be triggered to gain access to a program, online
service or an entire computer system. A Trojan horse is a harmful
program that is hidden inside apparently harmless programs or data.
Although a virus, a worm and a Trojan are different types of attacks,
they can be blended into one attack. For example, W32/Blaster and
W32/Sasser are blended attacks that feature a combination of a
worm and a Trojan.
Access Control Access control refers to procedures and controls that limit or detect
access. Access control attacks try to bypass validation checks in order
to access network resources such as servers, directories, and files.
Web Attack Web attacks refer to attacks on web servers such as IIS (Internet
Information Services).
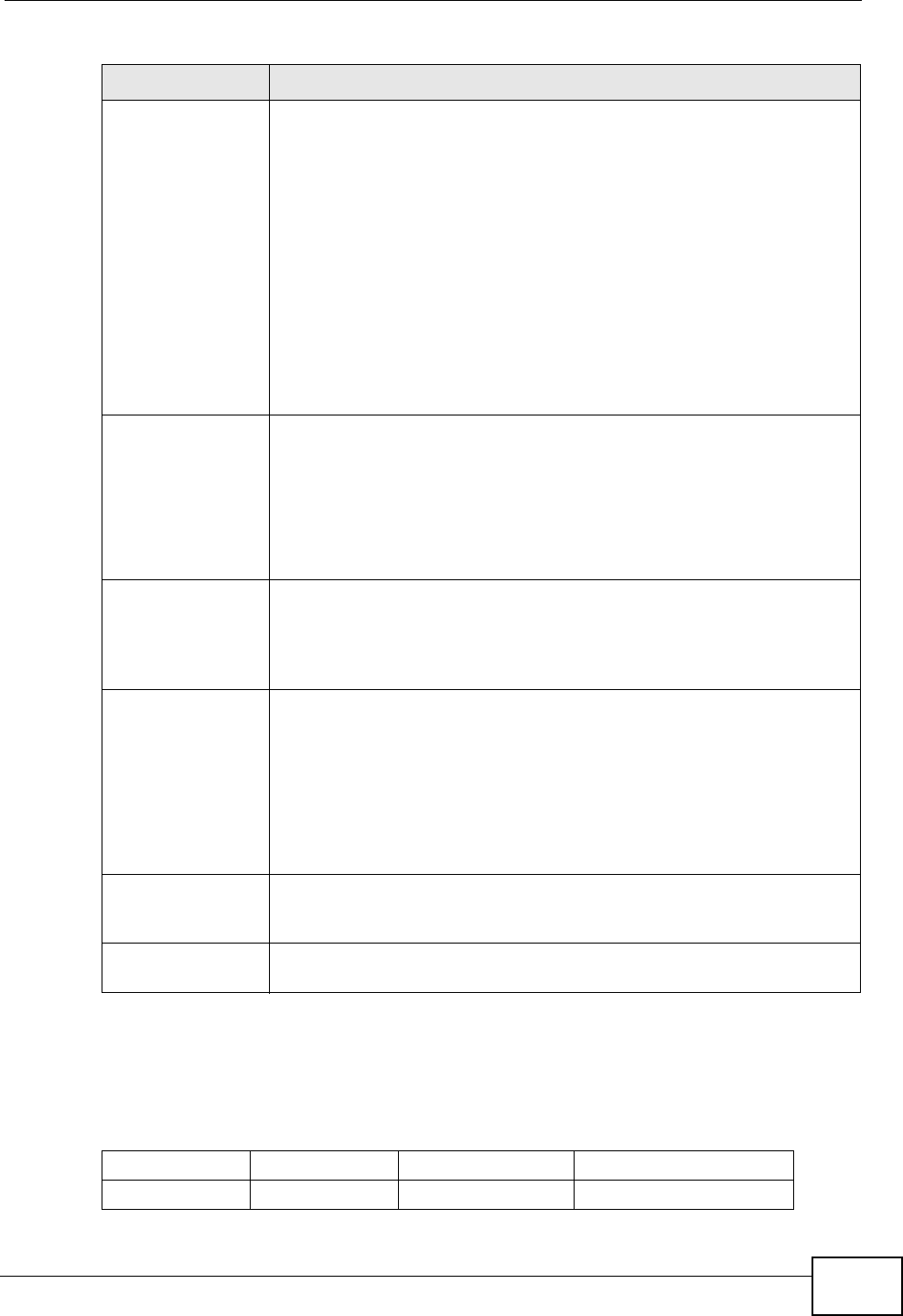
Table 146 Policy Types (continued)
POLICY TYPE DESCRIPTION
Table 147 IDP Service Groups
WEB_PHP WEB_MISC WEB_IIS WEB_FRONTPAGE
WEB_CGI WEB_ATTACKS TFTP TELNET


















