Content Filtering and Optimizing Scans
202
ProSecure Unified Threat Management (UTM) Appliance
3. Click Apply to save your settings.
Protect Against Email Spam
The UTM integrates multiple antispam technologies to provide comprehensive protection
against unwanted email. You can enable all or a combination of these antispam technologies.
The UTM implements these spam-prevention technologies in the following order:
1. Whitelist. Emails from the specified sources or to the specified recipients are not
considered spam and are accepted.
2. Blacklist. Emails from the specified sources are considered spam and are blocked.
3. Real-time blacklist. Emails from known spam sources that are collected by blacklist
providers are blocked.
4. Distributed spam analysis. Emails that are detected as spam by the NETGEAR Spam
Classification Center are either tagged or blocked.
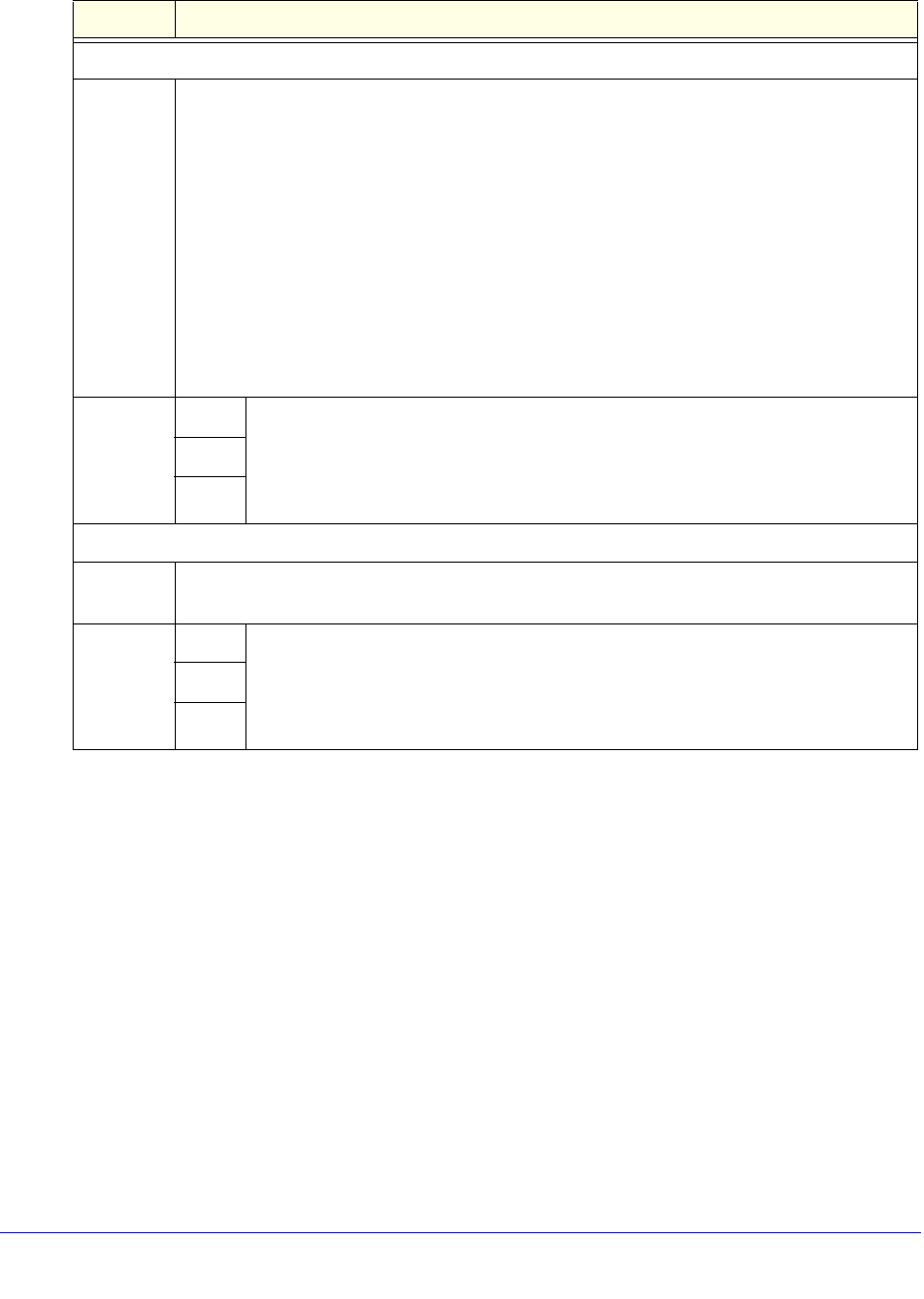
Filter by File Type
File
Extension
By default, the File Extension field lists the most common file extensions. You can manually
add or delete extensions. Use commas to separate different extensions. You can enter a
maximum of 40 file extensions. The maximum total length of this field, excluding the delimiter
commas, is 160 characters.
You can also use the drop-down list to add predefined file extensions from a specific category
to the File Extension field:
• None. No file extensions are added to the File Extension field. This is the default setting.
• Executables. Executable file extensions (exe, com, dll, so, lib, scr, bat, and cmd) are
added to the File Extension field.
• Audio/Video. Audio and video file extensions (wav, mp3, avi, rm, rmvb, wma, wmv, mpg,
mp4, and aac) are added to the File Extension field.
• Compressed Files. Compressed file extensions (zip, rar, gz, tar, and bz2) added to the
File Extension field.
Action SMTP From the drop-down list, select an action to be taken when an email attachment with
a file extension that is defined in the File Extension field is detected. The drop-down
list selections and defaults are the same as the ones for the Filter by
Password-Protected Attachments (ZIP, RAR, etc.) section that is described earlier in
this table.
POP3
IMAP
Filter by File Name
File Name Enter the file names that are detected. Use commas to separate multiple file names. For
example, to block the Netsky worm (which normally arrives as netsky.exe), enter netsky.exe.
Action SMTP From the drop-down list, select an action to be taken when an email attachment with
a name that is defined in the File Name field is detected. The drop-down list
selections and defaults are the same as the ones for the Filter by
Password-Protected Attachments (ZIP, RAR, etc.) section that is described earlier in
this table.
POP3
IMAP
Table 43. Email Filters screen settings (continued)
Setting Description


















