Virtual Private Networking Using IPSec, PPTP, or L2TP Connections
319
ProSecure Unified Threat Management (UTM) Appliance
8. Click Apply to save your settings. The IKE policy is added to the List of IKE Policies table.
Configure the ProSafe VPN Client for Mode Config Operation
When the Mode Config feature is enabled, the following information is negotiated between
the VPN client and the UTM during the authentication phase:
• Virtual IP address of the VPN client
• DNS server address (optional)
• WINS server address (optional)
The virtual IP address that is issued by the UTM is displayed in the VPN Client Address field
on the VPN client’s IPSec pane.
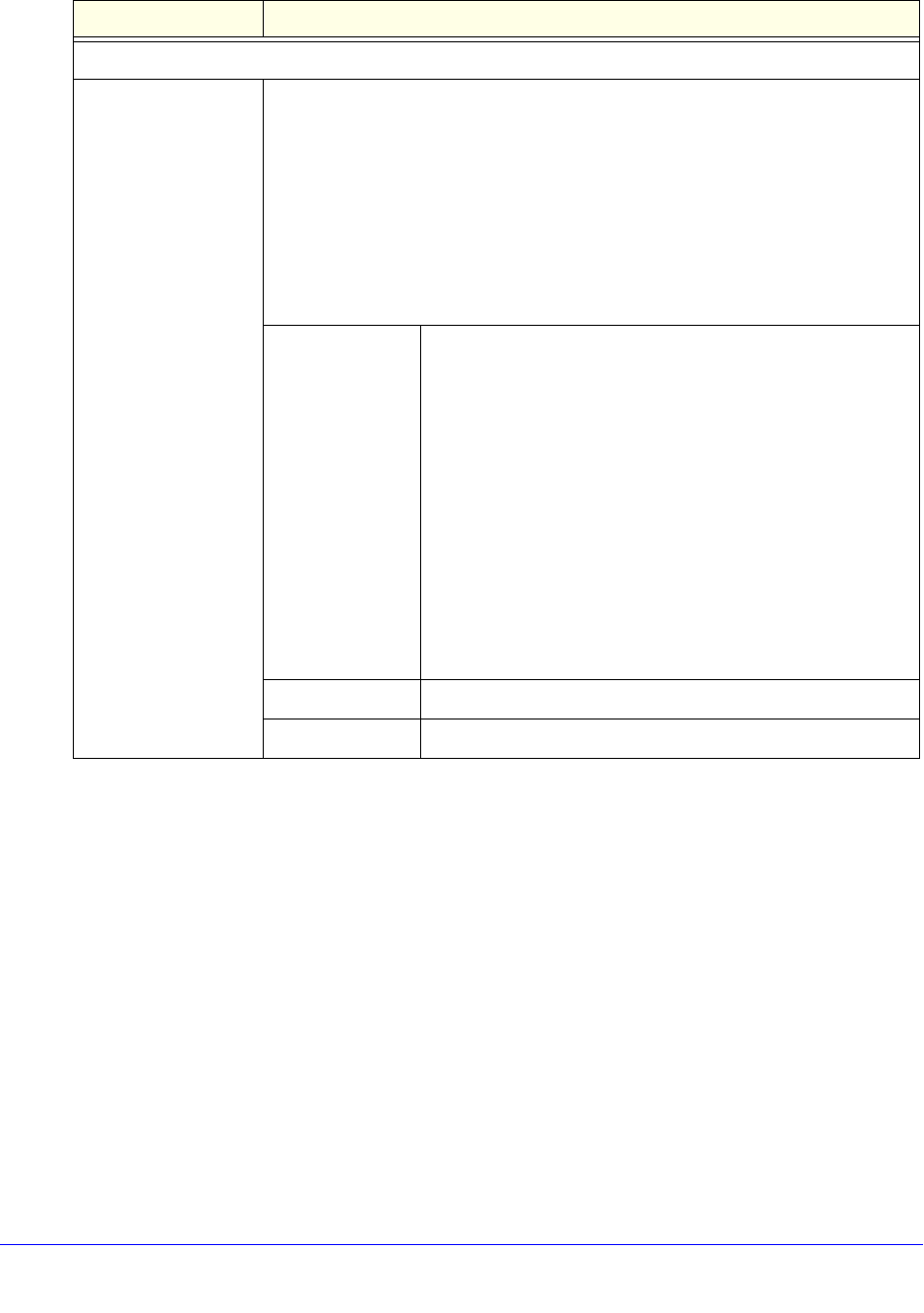
Extended Authentication
XAUTH Configuration
Note: For more
information about
XAUTH and its
authentication
modes, see Configure
XAUTH for VPN
Clients on page 309.
Select one of the following radio buttons to specify whether Extended
Authentication (XAUTH) is enabled, and, if enabled, which device is used to verify
user account information:
• None. XAUTH is disabled. This the default setting.
• Edge Device. The UTM functions as a VPN concentrator on which one or
more gateway tunnels terminate. The authentication modes that are available
for this configuration are User Database, RADIUS PAP, and RADIUS CHAP.
• IPSec Host. The UTM functions as a VPN client of the remote gateway. In this
configuration, the UTM is authenticated by a remote gateway with a user name
and password combination.
Authentication
Type
For an Edge Device configuration, from the drop-down list,
select one of the following authentication types:
• User Database. XAUTH occurs through the UTM’s user
database. You can add users on the Add User screen (see
User Database Configuration on page 310).
• Radius PAP. XAUTH occurs through RADIUS Password
Authentication Protocol (PAP). The local user database is
first checked. If the user account is not present in the local
user database, the UTM connects to a RADIUS server.
For more information, see RADIUS Client and Server
Configuration on page 310.
• Radius CHAP. XAUTH occurs through RADIUS
Challenge Handshake Authentication Protocol (CHAP).
For more information, see RADIUS Client and Server
Configuration on page 310.
Username The user name for XAUTH.
Password The password for XAUTH.
Table 78. IKE policy settings for a Mode Config configuration (continued)
Setting Description


















